Published by CasCom Ltd. | In partnership with Peplink

There’s a difference between a vehicle that’s online and a vehicle that’s operationally secure.
In Northern Canada, that distinction matters more than almost anywhere else. Public safety teams, government field crews, environmental monitors, and EMS personnel are increasingly relying on Starlink and LTE for connectivity in the field — and that’s a good thing. But connectivity alone isn’t a strategy. How that connection is controlled, segmented, and protected is what separates a functional setup from a secure one.
Most field deployments we encounter today are missing that second half.
The Setup That Looks Fine Until It Isn’t
The most common mobile connectivity configuration we see is straightforward: Starlink feeds directly into a vehicle’s onboard network, everything connects to it, and it works. Data flows, the radio checks in, someone streams a briefing — no issues.
Until there are issues.
When there’s no firewall, no traffic segmentation, no VPN tunnel back to command infrastructure, and no visibility into what’s traversing the link, you don’t have a secure network. You have a direct internet connection with wheels on it. Any device on that network — personal phones, unmanaged tablets, contractor equipment — shares equal standing with the most sensitive systems in the vehicle. Threats move freely. Sessions drop without warning. Nobody sees any of it until something breaks or something gets in.
For government agencies and public safety teams operating under data protection requirements, that’s not a theoretical risk. It’s a compliance and operational liability.
One Link Is a Single Point of Failure
Even if security isn’t the primary concern, single-link connectivity introduces a different kind of exposure. Starlink is strong technology, but satellite links are affected by terrain, weather, and congestion. When that one link fails, sessions drop — potentially mid-operation.
In the North, that’s not an edge case. It’s a regular condition.
Reliable field operations require a connectivity architecture designed around the assumption that any single link can fail at any time. Failover can’t be reactive. By the time a technician notices a dropped connection, the damage to an active operation may already be done.
What a Properly Designed Mobile Architecture Looks Like
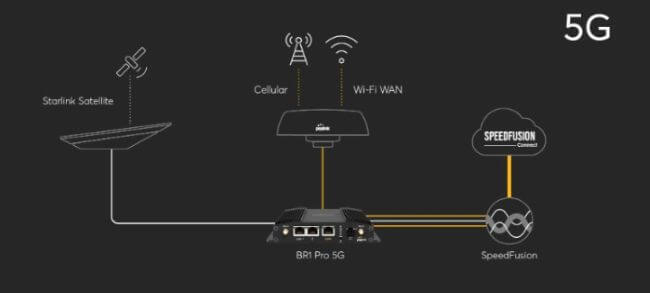
CasCom designs vehicle and field deployments around Peplink’s ecosystem specifically because it was built to solve this problem: maintaining secure, persistent connectivity across multiple unreliable links simultaneously.
Peplink SpeedFusion Bonding combines Starlink, LTE, and other available links into a single resilient connection. If one link degrades or drops, traffic shifts seamlessly across the remaining links — active sessions stay active, no manual intervention required. It’s not failover in the traditional sense. It’s true link bonding, where the whole is more reliable than any individual part.
SpeedFusion VPN ensures that traffic between the field and command infrastructure travels through an always-on encrypted tunnel. Sensitive databases, dispatch systems, and operational data don’t traverse the open internet — they move through a controlled, auditable path.
Hot Failover means that even when link composition changes, established sessions are preserved. An officer running a database query, a paramedic transmitting patient data, an environmental crew uploading telemetry — none of those sessions are interrupted by a link change.
Explore the full Peplink product line at peplink.com/products.
The CasCom Standard Mobile Build
For government, public safety, and enterprise deployments, CasCom implements mobile connectivity architectures using the following baseline configuration:
Core Router Peplink MAX BR2 Pro or MAX Transit Pro — purpose-built for demanding mobile environments with multi-WAN support, ruggedized hardware, and centralized management capability.
Connectivity Stack
- Starlink as the primary high-throughput link
- Dual LTE/5G with carrier diversity for resilient failover
- Wi-Fi as WAN for situational or supplementary use
Network Controls
- Segmented networks isolating operational traffic from general-use devices
- Traffic prioritization ensuring critical applications are never competing with background use
- Always-on encrypted tunnels to command and control infrastructure
Management and Visibility
- Centralized monitoring with remote configuration enforcement
- Full event logging and usage visibility
- Incident traceability across all connected devices
This isn’t a premium upgrade. It’s the baseline for responsible field connectivity.
Who This Protects and How
Policing and Public Safety Secure, persistent access to law enforcement databases without exposing endpoints to the open internet. Reliable video and telemetry transmission during transit. Maintained session continuity during active operations.
Environment and Natural Resources Stable communications in wildfire response, remote survey operations, and areas where single-link reliability is routinely compromised by terrain. Controlled data flow from field devices back to operational systems.
Healthcare and EMS Protected patient data in transit, with connectivity that doesn’t drop mid-transport. Consistent performance under load, regardless of link conditions.
Government and Territorial Operations Alignment with federal and territorial data protection frameworks. Centralized oversight of field network activity. Reduced exposure from unmanaged or personally-owned devices sharing operational networks.
Private Sector — Mining, Construction, Remote Enterprise Lower operational risk at remote worksites. Improved compliance posture for regulated industries. Connectivity that supports rather than limits field operations.
The Architecture Is the Product
Starlink is an excellent component. LTE is an excellent component. Neither one is a complete solution on its own, and neither one becomes secure just by being deployed.
What determines the reliability and security of a mobile deployment is the architecture surrounding those components — how links are bonded, how traffic is prioritized, how data is encrypted, how the network is segmented, and how all of it is monitored over time.
That’s where most field deployments fall short, and it’s where CasCom focuses.
CasCom + Peplink: Built for Northern Conditions
CasCom has been delivering technology and communications solutions across Northern Canada since 1996. As a Peplink partner, we design, deploy, and support secure mobile connectivity architectures specifically for the operational conditions of Northern environments — remote terrain, extreme weather, limited on-site technical support, and high stakes for the teams depending on that infrastructure.
We don’t deploy hardware and walk away. We architect for resilience, implement with security as a baseline requirement, and provide ongoing oversight so that when conditions change — and in the North, they always do — your operations don’t miss a beat.
Ready to talk about your mobile or field connectivity requirements?
Contact CasCom Ltd. 📞 867-765-2020 📧 info@cascom.ca 🌐 cascom.ca
CasCom Ltd. — Enabling the North. Headquartered in Yellowknife, NT. Peplink products and SpeedFusion technology: peplink.com